Understanding what these proposed changes really mean for small health care organizations — and why the biggest risk isn't the regulations themselves
A Note to Rural Health Care Leaders
This article contains tough love — but it comes from a place of deep respect and genuine concern. We know you're not in rural health care for the money — you could make more elsewhere. You're here because you care about your community. We share that mission, which is why we believe in giving you straight talk about risks and challenges. Our role is to help you see potential blind spots before they become serious problems.
The current rural health care climate is extraordinarily challenging, with financial pressures, regulatory demands, staffing shortages, and technology requirements converging all at once. We understand that rural health care leadership faces immense pressure from multiple directions simultaneously — pressures that others outside your world simply cannot comprehend.
Our mission at visuaFUSION is helping rural health care organizations keep their doors open while maintaining their independence. Everything we share in this article stems from that commitment. You'll read about common challenges we see across the industry, and we want you to know we recognize these aren't personal failures — they're systemic issues affecting organizations just like yours.
We ask that you approach this article with an open mind. The goal isn't to criticize, but to illuminate risks that may not be visible until it's too late. Your community depends on you staying operational, compliant, and financially viable. Sometimes that requires taking a hard look at practices that may have worked in simpler times but create vulnerabilities in today's complex regulatory and threat environment.
The proposed HIPAA Security Rule changes were supposed to take effect January 6, 2025. While the new administration has paused these updates for now, the writing is on the wall: stronger cybersecurity requirements are coming. But here's what most health care leaders don't realize — the biggest challenges aren't the new rules themselves. They're the gaps that already exist in how most small health care organizations approach IT security.
You run a health care organization. That means your data is as valuable as Fort Knox to cybercriminals, right? Your regulatory requirements are the same whether you're a 25-bed rural hospital or Mayo Clinic. But are your IT practices designed for what you actually are — a health care organization — or are they still built like a small business?
What the Proposed Changes Actually Mean
The proposed updates aren't revolutionary — they're clarifications of what HIPAA already requires. Think of it like this: if HIPAA was a bridge, these changes aren't building a new bridge. They're just putting up signs that say "Bridge Weight Limit: 10 Tons" instead of assuming everyone knows heavy trucks shouldn't cross.
The Big Picture Changes
Universal Implementation: All HIPAA Security Rule specifications become mandatory. No more "addressable" versus "required" distinctions. (45 CFR 164.306(d)(3))
Documentation Everything: Written policies for all security procedures, including AI systems. Think of documentation like medical charts — if it's not documented, it didn't happen. (45 CFR 164.316(b)(1))
Asset Inventory: Annual technology inventories, including all AI software handling patient data. It's like knowing where all your medical equipment is — basic, but surprisingly uncommon.
Risk Analysis: Comprehensive assessments including AI systems, covering what patient data they access, who sees the output, and how they affect data security. (45 CFR 164.308(a)(1)(ii)(A))
24-Hour Notifications: For access changes and contingency plan activations. Quick response times — kind of like medical emergencies, but for data.
Mandatory Technical Controls: Encryption at rest and in transit, multi-factor authentication (kind of like requiring two signatures for controlled substances), anti-malware protection, and network segmentation (like having separate areas for different hospital departments). (45 CFR 164.312(a)(2)(iv) and 45 CFR 164.312(e)(2)(ii))
Regular Security Testing: Vulnerability scans every six months, penetration testing annually. It's like regular equipment maintenance — prevention instead of reaction.
But here's the reality most rural health care leaders face: these aren't new requirements. They're clarifications of what HIPAA has always required.
The Truth About "Addressable" Requirements
Let's clear up the biggest misconception in health care IT: "addressable" never meant optional. It meant you had to either implement what was listed, or document why it wasn't reasonable for your situation and show how you achieved equivalent protection another way.
How many organizations actually did that analysis and documentation? Very few. Most treated "addressable" as a skip button.
Current HIPAA regulations already call for strong security practices. The problem isn't the regulations — it's that many organizations, especially smaller ones, never fully implemented what was already required. Does your organization have documented security policies for every system that touches patient data? Can you prove your current security measures are working? If not, you're not just unprepared for new requirements — you may already be out of compliance with existing ones.
The Real Challenge: Operating as a Health Care Organization, Not a Small Business
Your organization may be small by employee count, but you're operating in a field that requires enterprise-level security. It's like being a small-town bank — your size says "small business," but your responsibilities require enterprise solutions.
This creates a unique challenge. You need enterprise-grade security, but you don't have enterprise budgets or enterprise IT teams. You probably have one IT person, maybe two. They're likely handling everything from password resets to major system implementations. Are they also trained in HIPAA compliance, risk analysis, and incident response planning?
Most small health care organizations still run their IT like a small business: reactive, informal, and focused on keeping systems running rather than keeping them secure. But cybercriminals don't care about your size — they see patient data, and that's worth millions on the dark web.
The AI Wild West: When "Convenience" Creates Catastrophic Risk
Before we talk about traditional vendor problems, we need to address the elephant in the room: artificial intelligence in health care is currently the wild west. AI could bite a small health care organization that isn't diligent about HIPAA security like a rattlesnake hiding under a blanket.
Here's a real story that happened recently: A CEO of a rural hospital saw an advertisement for a "free" AI note-taking tool. The idea seemed perfect — the AI would automatically take notes during meetings so the CEO could pay better attention to what was being discussed.
Within 10 minutes, the CEO had followed the ad and connected this third-party AI tool to his Microsoft Teams account. (Quick note: by default, Microsoft Teams allows anyone in your organization to authorize third-party apps — something your IT team should change immediately.)
A few days later, we were in a Teams meeting with this CEO, troubleshooting an HL7 interface problem (HL7 is kind of like a translator that helps different medical systems talk to each other). One vendor was sharing his screen with a notepad window open, showing an HL7 message so the other vendor could track down an error in their system.
The CEO joined the meeting for an update. His AI note-taker automatically joined too.
The AI immediately began analyzing what was displayed on the screen using intelligent text recognition. It captured the patient's name, date of birth, medical record number, type of study — everything visible in that HL7 message. All of this patient information appeared in the AI's meeting notes.
What happened next was a HIPAA data breach.
Here's why: HIPAA requires a Business Associate Agreement (BAA) for any vendor that handles, stores, processes, or transmits protected health information (45 CFR 164.502(e)). When the AI processed that patient information through its cloud servers without a BAA in place, it created a breach caused by the covered entity's own negligence.
HIPAA violation fines can range from $141 to $2,134,831 per violation depending on the level of culpability, with annual maximum penalties of $1,919,173 per calendar year. For a small rural hospital, even a modest fine could be devastating.
When we investigated this particular AI note-taker's terms, we discovered their free tier didn't offer BAAs. This is very common with free software — and it gets worse. Many of these AI note-takers require you to subscribe to their highest tier plan (typically $29-$50 per user per month) before they'll even consider signing a BAA. Many also require minimum user commitments — often 10 users — meaning a rural health care organization could face a $3,000+ annual bill to use these "free" solutions safely.
The "I Don't Deal with PHI" Trap
Since this incident, we've heard other CEOs and COOs say, "I don't deal with patient information, so this wouldn't be an issue for me." They're partially right — until they aren't. And when it matters, it's too late.
The safest approach for any health care organization is to treat all systems as if they contain patient information — because they truly could, at some point, indirectly or unintentionally.
Consider these scenarios that happen every day:
- Web-based medical software caches images and data locally on computers
- Users screenshot medical applications to send with support tickets
- Staff edit Word documents containing patient information (creating local auto-recovery files)
- Medical images or reports get temporarily downloaded for viewing
The moment any of this happens, that device becomes a system containing protected health information under 45 CFR 164.304, subject to all HIPAA security requirements.
This is why every computer in a health care environment — including those used by maintenance, housekeeping, and administration — should be encrypted and managed as if it contains patient data. Because it very well might.
The Software Intake Solution
This AI note-taker incident highlights why every health care organization needs a formal software intake process with IT involved from the beginning. This applies to all software: desktop applications, mobile apps, web services, and especially "free" tools that seem convenient.
Two critical warnings about free software in health care:
- Most free software licensing is for personal use only — not business use
- Free tiers rarely include BAAs or HIPAA compliance features
Your legal team should review licensing terms for all software, but especially free tools. (Open source software is typically fine on both counts, as long as proper risk analysis is performed.)
Does your organization have a process where IT evaluates every piece of software before it's used? Can you guarantee no one in your organization is using unauthorized apps or services that might process or have line of sight to patient information? If not, you have unknown risks that could trigger compliance violations at any moment. Why would you ever approve money spend on an application IT evaluates and finds out completely opens you up to HIPAA security risks? Give them the chance to save you in advance
Here is an example of the application intake process we help clients implement:
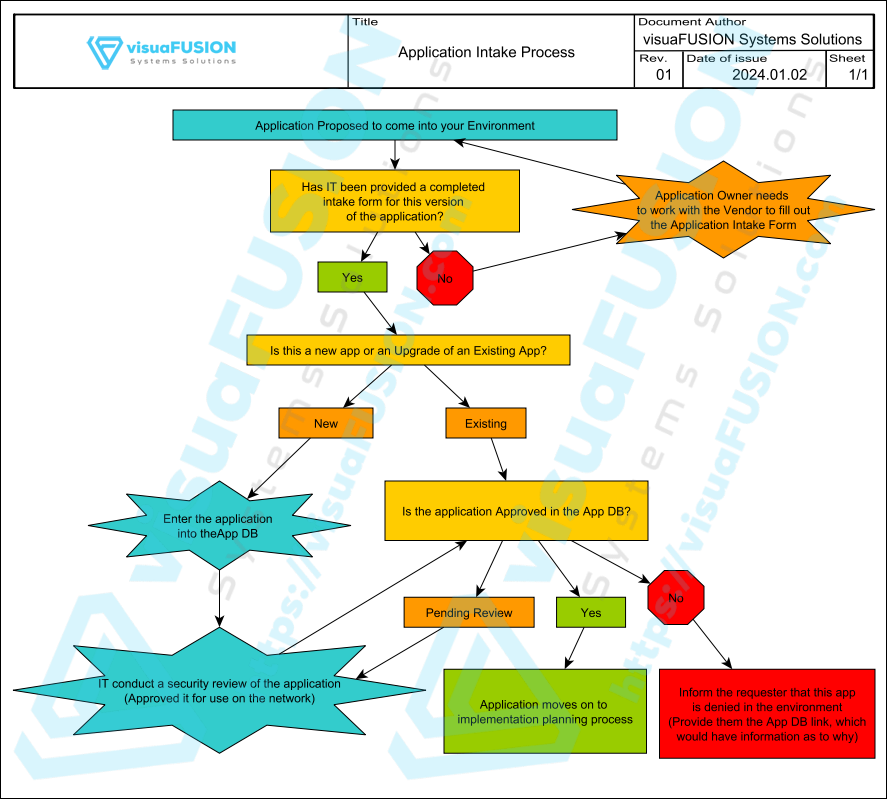
As you can see, the process involves IT early on, the first question asked is an IT question, asking if an application intake form (a document typically used to gather information about an application) has been completed, which can be evaluated to determine the IT lift and security posture of the software. The process involves a security review prior to moving on to any purchase decision. 99.9% of applications have competitors out there, and this process can not only save you from purchasing a security nightmare, but also give you bargaining leverage. If you're going to pay money for software, you may as well arm yourself with the knowledge to be able to come to the table and say "We'll move forward with the purchase, with the agreement that XYZ software company will mitigate the following findings within 90 days of implementation."
The Traditional Vendor Problem: When Security Takes a Back Seat to Convenience
Beyond the AI challenge, many traditional health care IT vendors — especially those selling to smaller organizations — have been getting away with poor security practices for years. They use "FDA requirements" or "industry standards" as excuses for systems that any security expert would red-flag immediately.
Take medication dispensing systems as an example. We recently reviewed documentation from a leading medication dispensing vendor (you probably know which one — they have a large portion of the market share). Their requirements for domain integration would make any security professional's hair stand on end:
- Disabling User Account Control (UAC) — kind of like removing all safety locks from medical equipment
- Disabling Windows Firewall or creating "allow all" rules — like leaving all doors unlocked
- Blocking Group Policy inheritance — preventing your organization from enforcing its own security standards
- Requiring local administrative accounts — giving every system the keys to everything
- Running scripts that disable domain security policies entirely
These requirements create massive security vulnerabilities. Yet under the PATCH Act of 2022 and updated FDA guidance, medical device manufacturers are actually required to "maintain plans for regular and emergency software updates" and "strengthen cybersecurity design" for their devices. The FDA isn't requiring weak security — many vendors are just using regulatory compliance as a smokescreen for poor security practices.
If you're using a big-name medication dispensing system, check whether yours requires these types of security compromises. If it does, you're accepting significant risk before you even know what that risk is.
The Culture Shift That Changes Everything
Most small health care organizations follow a dangerous pattern: department heads purchase software, then bring IT in to "make it work." By this time, security vulnerabilities are already accepted — before they're even evaluated.
This approach is itself a security vulnerability. Would you let a department head purchase medical equipment without involving clinical staff in the safety evaluation? Of course not. So why do many organizations purchase software that handles patient data without involving IT in security evaluation?
But here's an uncomfortable truth: health care leaders are often too quick to side with department heads who "just want it done," telling IT to "do it anyway" when IT presents any resistance at all.
Becoming secure requires a culture and mindset shift that needs the full backing of health care administration. Convenience should never trump security. Small health care organizations are health care organizations, not donut shops. You handle the same sensitive data as Mayo Clinic — your security should reflect that reality.
The Administrative Support That Makes Security Work
Strong security policies are worthless if administration overrides them constantly under pressure from managers and department heads. Imagine having a loved one in a hospital where you discovered administration approved every security exception, leaving the environment completely exposed to cyber threats. That would place patient safety in question — and you wouldn't feel great about that.
Your IT team and HIPAA Security Officer are doing their job when they present security concerns. They have your organization's best interests at heart, and you've entrusted them to protect patient data. When they push back on a request, it's not obstruction — it's protection.
Another hard truth: if you don't trust their technical and security opinions, perhaps someone else should be in charge of HIPAA security in your organization. Their voice should be the most weighted voice in security decisions — your organization's HIPAA compliance depends on it.
The Right Way to Handle Security Exceptions
Not every department request can be accommodated exactly as asked, but that doesn't mean the answer is always "no." Strong security policies should include a formal exception process that requires:
- Documented approval from administration
- Risk analysis outlining specific threats and impacts
- Temporary timelines with correction plans
- Regular review of active exceptions
Security policy exceptions are temporary measures that acknowledge "we're aware of this risk and are working to mitigate it." They're not permanent workarounds or permission to ignore security requirements.
The solution requires a culture shift: partnering with IT from day one. Every software purchase, every system upgrade, every new vendor relationship should include IT security evaluation before any commitments are made. IT should have weighted input in software decisions, not just implementation responsibilities.
A phrase visuaFUSION's CEO, Sean Huggans, uses frequently in health care systems engineering is: "How can we do it right, instead of right now?" By supporting your IT resources and giving them administrative backing, you ensure your organization is doing it right, instead of just right now.
Your IT team (even if it's one person) becomes a strategic partner, not just a support function. They help evaluate vendors, assess risks, and ensure new systems fit your security model instead of compromising it.
Does your organization have a formal application intake process? Can your IT team evaluate security requirements before purchases are approved? If not, you're making decisions in the dark about systems that could expose your entire organization to cyber threats.
Rural health care organizations need strategic partners who will share hard truths like these — partners willing to clearly outline risks so administration can make informed decisions. In your position, you need advisors who will respectfully challenge ideas when patient safety and organizational security are at stake. Another voice simply saying "yes" to every request isn't strategic partnership — it's enablement of risk.
A successful culture shift to a secure environment requires not just technical solutions, but workflow and people solutions. Most importantly, it requires administrative buy-in and support — every single day.
Breaking Free from Vendor Lock-In
Here's something many small health care organizations don't realize: you have options. You don't have to accept vendors who dictate security standards to you instead of working within your requirements.
For medication dispensing, there are vendors who specialize in rural health care and work within standard security environments. These vendors often offer 40-70% cost savings over big-name competitors, with products designed to play nicely with modern, secure IT infrastructure.
The difference is striking. Where most vendors in this space say "this is how we require things — we won't flex to meet your requirements," alternatives exist that are happy to work within your security framework. Some even design their systems so the controlling computer can be replaced by local IT as needed, rather than requiring expensive cabinet replacements when technology upgrades are needed.
This translates to huge savings — not just 40-70% upfront, but even more over time. Replacing an $800 workstation every few years versus replacing a $40,000 cabinet makes a dramatic difference in long-term costs.
It's up to YOU to hold your medical vendors accountable. Demand better security practices, and be willing to take your business elsewhere if they're willing to introduce risk into your environment while charging you a premium. You're not just a customer — you're the decision-maker for your organization's security posture.
Are you locked into expensive contracts with vendors who compromise your security? Have you explored alternatives that could save money while improving your security posture?
The Economics: Why This Hits Rural Health Care Hardest
These proposed changes come at the worst possible financial time for rural health care. The One Big Beautiful Bill could force closure of 18-20% of rural hospitals through Medicaid cuts and reduced support programs. Combined with existing budget pressures, new compliance costs feel like throwing gasoline on a fire you're already struggling to contain.
But here's what many organizations miss: increased regulations create increased costs for vendors too. Those costs get passed down to customers, and they disproportionately impact smaller organizations. Large health systems can spread compliance costs across thousands of beds. A 25-bed hospital absorbs the same vendor cost increases with a fraction of the revenue base.
HIPAA doesn't scale based on organization size, and it shouldn't. But the economic impact does scale — and it hits small organizations much harder. This makes strategic vendor relationships and efficient IT practices more critical than ever.
How many of your current vendor relationships were chosen primarily on price, without considering long-term security and compliance costs? Are you paying premium prices for substandard security because you're locked into contracts with vendors who see small organizations as "small potatoes"?
Working with the Right Partners
The good news? Some vendors understand rural health care's unique challenges and price their solutions accordingly. Look for technology partners who:
- Specialize in small health care organizations
- Work within your security requirements instead of dictating them
- Offer group pricing or collective discounts for small organizations
- Understand that rural health care organizations need enterprise-grade security at small-organization prices
Small organizations supporting other small organizations creates a partnership model where everyone succeeds. Large vendors often lock their best pricing behind volume commitments that small organizations can't meet. Vendors who focus on rural health care understand your reality and price accordingly.
Does your current vendor lineup include partners who truly understand small health care? Are you working with companies who see supporting rural health care as their mission, or just a market segment?
The Technical Reality Check
If you're still running Windows Pro across your environment, paying for separate antivirus, encryption, and management tools, and handling security through spreadsheets and hope — you're not just unprepared for proposed changes. You're operating with significant compliance gaps right now.
Modern enterprise solutions designed for small health care can actually reduce total costs while improving security and compliance. Tools that were once only available to large health systems are now accessible to small organizations through the right partnerships.
The question isn't whether you can afford to upgrade your approach to IT security. The question is whether you can afford not to. One successful cyberattack, one compliance violation, or one system failure can cost more than years of proper preventive investment.
Can you easily prove HIPAA compliance across your organization today? Do you have centralized control over encryption, access management, and security policies? If not, you're already behind where you need to be.
The Strategic Path Forward
Strong IT security isn't just about compliance — it's about operational resilience. When your systems are properly secured, managed, and documented, they're also more reliable, easier to maintain, and less likely to fail when you need them most.
The organizations that will thrive through these regulatory changes are those that view IT security as a strategic advantage, not just a compliance checkbox. They partner with vendors who understand their unique challenges. They involve IT in decision-making from the beginning. And they work with strategic partners who can help translate enterprise-level security into models that work at their scale.
This isn't about becoming a different organization. It's about operating your current organization with the tools and practices that match your actual responsibilities and risks. You're already a health care organization — now it's time to make sure your IT practices reflect that reality.
The proposed HIPAA changes may be paused, but the underlying need for stronger cybersecurity isn't going away. The organizations that get ahead of these changes now will find compliance easier, costs lower, and operations more resilient when the final requirements do take effect.
Moving Forward with Confidence
If this article has raised questions about your current IT security posture, vendor relationships, or compliance readiness, you're not alone. Most small health care organizations discover gaps when they take an honest look at their current practices.
The key is working with partners who understand your world. visuaFUSION Systems Solutions specializes exclusively in small health care organizations across the United States. We work with community clinics, rural hospitals, long-term care facilities, and behavioral health centers — organizations that need enterprise-grade security at a scale and price that makes sense for their reality.
Our approach is simple: we focus on IT so you can focus on patients. We help small health care organizations manage increasing IT requirements and regulations without breaking budgets or compromising independence. We're not here to own your organization — we're here to help you manage IT challenges while maintaining your autonomy.
Our team understands the vital role small health care organizations play in their communities, and we've seen firsthand the challenges they face with rising IT costs and compliance requirements. We provide the same advanced IT resources and expertise that large health systems have, tailored specifically for small health care organizations.
Whether you need strategic IT planning, HIPAA security policies and procedures, vendor evaluation, or comprehensive managed services, we translate enterprise complexity into solutions that work at your scale. Because you deserve the same level of IT sophistication as large health systems — without compromising your independence or your budget.
visuaFUSION Systems Solutions is an IT strategic partner focused exclusively on rural and small health care organizations in the United States. For more information about how we help organizations like yours manage IT challenges while maintaining independence and controlling costs, visit visuafusion.com or call (308) 708-7490.
- Log in to post comments